API Testing: Types, Strategies & Best Practices (2026)
Master API testing with this complete guide. Learn testing types, strategies, security checks, and tool picks to ship reliable APIs.
Read more
All Articles

Security Testing Tools and its Types
Essential security testing tools and their types, including SAST, DAST, and IAST, to protect your software from vulnerabilities.
security testing
API Security Checklist: 12 Steps to a Secure API
Secure your APIs with this comprehensive 12-step checklist, covering authentication, data protection, monitoring, and more.
API security
8 API Testing Tools You Should Know
Essential API testing tools that enhance reliability, security, and performance in modern software development workflows.
API testing
API Security Best Practices for 2026: Gateway/WAAP, OAuth 2.1, Workload Identity & CI/CD Recipes
Protect your APIs with 15 proven security practices: authentication, rate limiting, input validation, encryption, and real-time monitoring.
API security
SQL Injection (SQLi): Types, Examples & Prevention
Understand all SQL injection types with real examples. Prevent SQLi using parameterized queries, WAF rules, and a step-by-step detection playbook.
SQL Injection
API Inventory: Why You Need One & 10 Steps to Build It
Build a complete API inventory in 10 steps. Reduce shadow API risk, improve security posture, and stay compliant with this actionable guide.
API inventory
Broken Function-Level Authorization: Prevention
What is broken function level authorization (BFLA)? Learn how this OWASP API vulnerability works, real-world examples, and how to prevent it.
Broken Function-Level Authorization
10 LLM Security Tools
Essential security tools designed to protect Large Language Models from vulnerabilities like prompt injection and data leaks.
LLM security
API Attacks: Real-World Examples, OWASP Risks & Prevention
Most common API attacks, real-world breach examples, OWASP Top 10 risks, and practical defenses to secure APIs end-to-end.
API attacks
Top 12 Vulnerability Scanning Tools
Compare the best vulnerability scanning tools: Nessus, Qualys, OpenVAS, Qodex and more. Features, pricing, and OWASP compliance coverage.
vulnerability scanning
IAST vs DAST: Key Differences & How to Choose
IAST vs DAST compared: accuracy, CI/CD fit, false positives, and setup complexity. Use our decision framework to pick the right AppSec approach.
IAST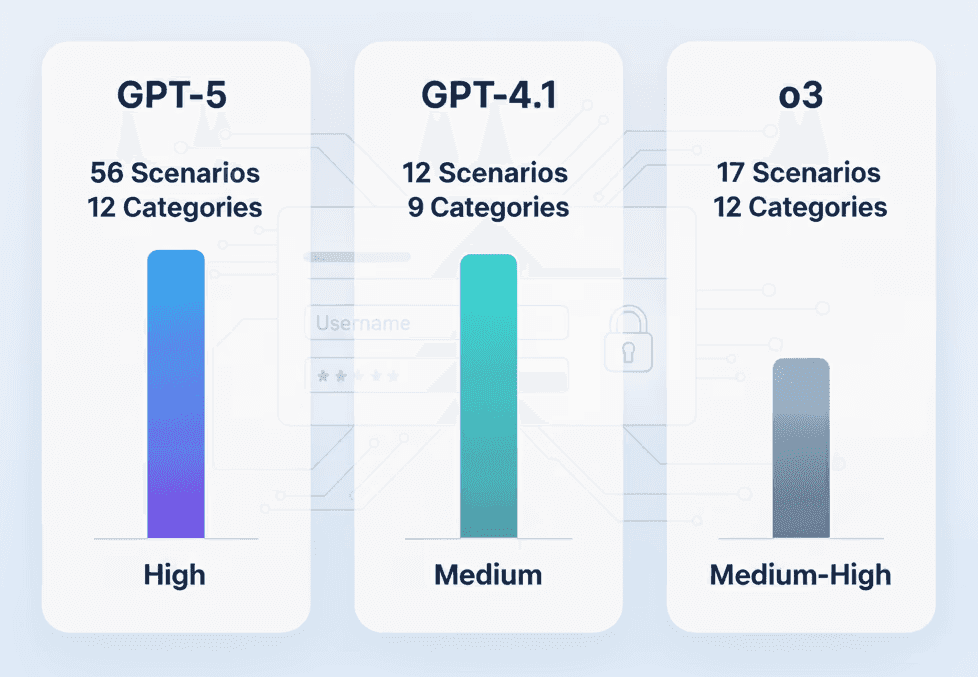
GPT-5 vs O3 vs GPT-4.1 for Penetration Testing
We tested GPT-5, O3, and GPT-4.1 on real pen testing tasks. See which AI model finds more vulnerabilities and produces actionable reports.
GPT-5 penetration testing