Api Security
Explore 29 articles about Api Security. Expert tips, guides, and strategies for API testing and automation.

API Security Best Practices for 2026: Gateway/WAAP, OAuth 2.1, Workload Identity & CI/CD Recipes
Protect your APIs with 15 proven security practices: authentication, rate limiting, input validation, encryption, and real-time monitoring....
API Attacks: Real-World Examples, OWASP Risks & Prevention
Most common API attacks, real-world breach examples, OWASP Top 10 risks, and practical defenses to secure APIs end-to-end....
API Fuzz Testing Guide: Find Hidden Vulnerabilities in 2026
Master API fuzz testing to uncover hidden security vulnerabilities before attackers do. Complete guide with tools, best practices, and CI/CD...

API Security 101: Foundations, Threats & Best Practices
API security fundamentals: OWASP Top 10, CI/CD integration, GraphQL/gRPC, and real breach lessons to secure your APIs from day one....

API Security Checklist: 12 Steps to a Secure API
Secure your APIs with this comprehensive 12-step checklist, covering authentication, data protection, monitoring, and more....
API Security Checklist 2026: 12 Steps Every Developer Needs
Follow this 12-step API security checklist (2026 edition) with threat modeling, real examples, PDF, and best practices for robust API...
API Security Testing: OWASP Top 10, Tools & Checklist
Complete guide to API security testing, OWASP Top 10 risks, testing tools, checklists, and how to secure your APIs against...
API Security Trends
Top API security trends for 2026: bot attacks up 372%, shadow APIs, AI-driven threats, and zero-trust strategies to protect your...
Common API Security Vulnerabilities & Solutions (2026 Guide)
Top API vulnerabilities like BOLA, mass assignment, GraphQL abuse, and JWT misuse. See practical solutions, OWASP Top 10 mapping, and...

Top 10 Cybersecurity Challenges Facing FinTech in 2026
The 10 biggest cybersecurity threats facing fintech in 2026: AI-driven attacks, API exploits, data breaches, and compliance gaps with actionable...
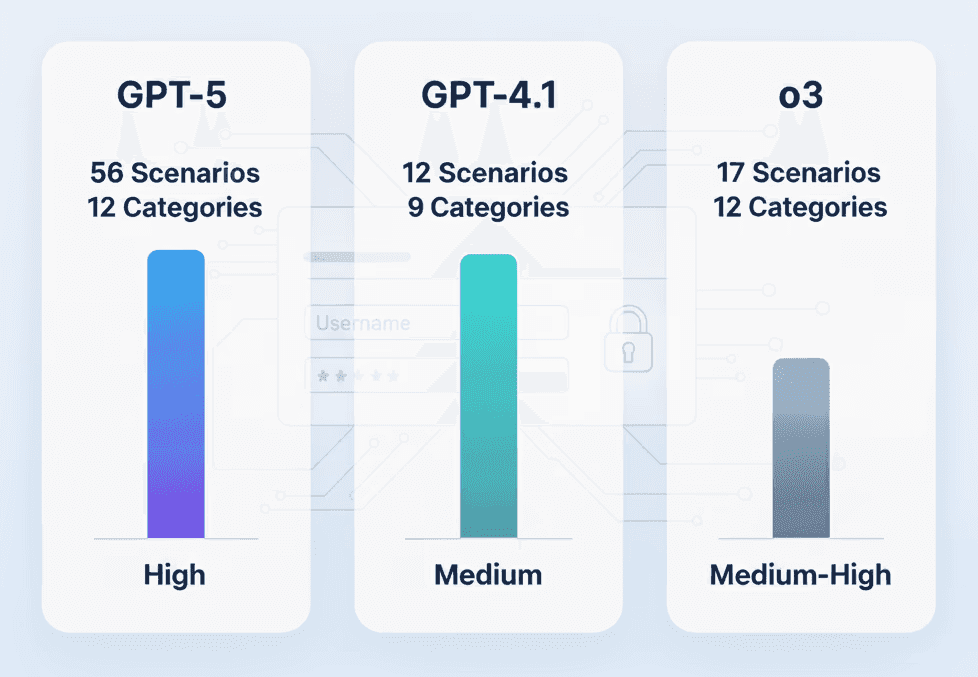
GPT-5 vs O3 vs GPT-4.1 for Penetration Testing
We tested GPT-5, O3, and GPT-4.1 on real pen testing tasks. See which AI model finds more vulnerabilities and produces...
How to Get a Rugcheck API Key and Start Using the API
Step-by-step guide to getting a Rugcheck API key and using the Rugcheck.xyz API for token audits, rug pull detection, and...
MD5 vs SHA-256, Key Differences, Security & When to Use Each
Compare MD5 and SHA-256 hash algorithms. Learn the key differences in security, speed, and use cases to choose the right...
OWASP API Top 10 (2023): Complete Guide with Tests & Fixes
Complete guide to OWASP API Security Top 10 risks. Covers BOLA, broken auth, SSRF with real exploit examples, test cases,...

Top 10 Rapid7 Alternatives for Cybersecurity
Comparing 10 Rapid7 alternatives for VM, AppSec, and SIEM. Side-by-side pricing, pros/cons for Tenable, Qualys, CrowdStrike, and more....

Security Testing Tools and its Types
Essential security testing tools and their types, including SAST, DAST, and IAST, to protect your software from vulnerabilities....
SHA-1 vs SHA-256, Key Differences, Security & When to Use Each
Compare SHA-1 and SHA-256 hash algorithms. Learn the key differences in security, performance, and use cases to choose the right...
SHA-256 vs SHA-512, Key Differences, Performance & When to Use Each
SHA-256 vs SHA-512 compared: output size, speed benchmarks, security strength, and when to pick each hash algorithm. Decision table included....
SQL Injection (SQLi): Types, Examples & Prevention
Understand all SQL injection types with real examples. Prevent SQLi using parameterized queries, WAF rules, and a step-by-step detection playbook....

Top 10 DAST Tools for 2026
Top DAST tools of 2026 for effective API security testing, integration, and automation in modern development workflows...
What Is DevSecOps? Definition and 10 Best Practices
10 essential DevSecOps practices to embed security into your CI/CD pipeline. Actionable checklist for shift-left security in 2026....

Top 12 Vulnerability Scanning Tools
Compare the best vulnerability scanning tools: Nessus, Qualys, OpenVAS, Qodex and more. Features, pricing, and OWASP compliance coverage....
Top API Security Vendors: Compare Features & Services
Compare the top API security vendors for 2026: Qodex, Akamai, Salt Security, and Imperva. Features, pricing, and OWASP coverage side...
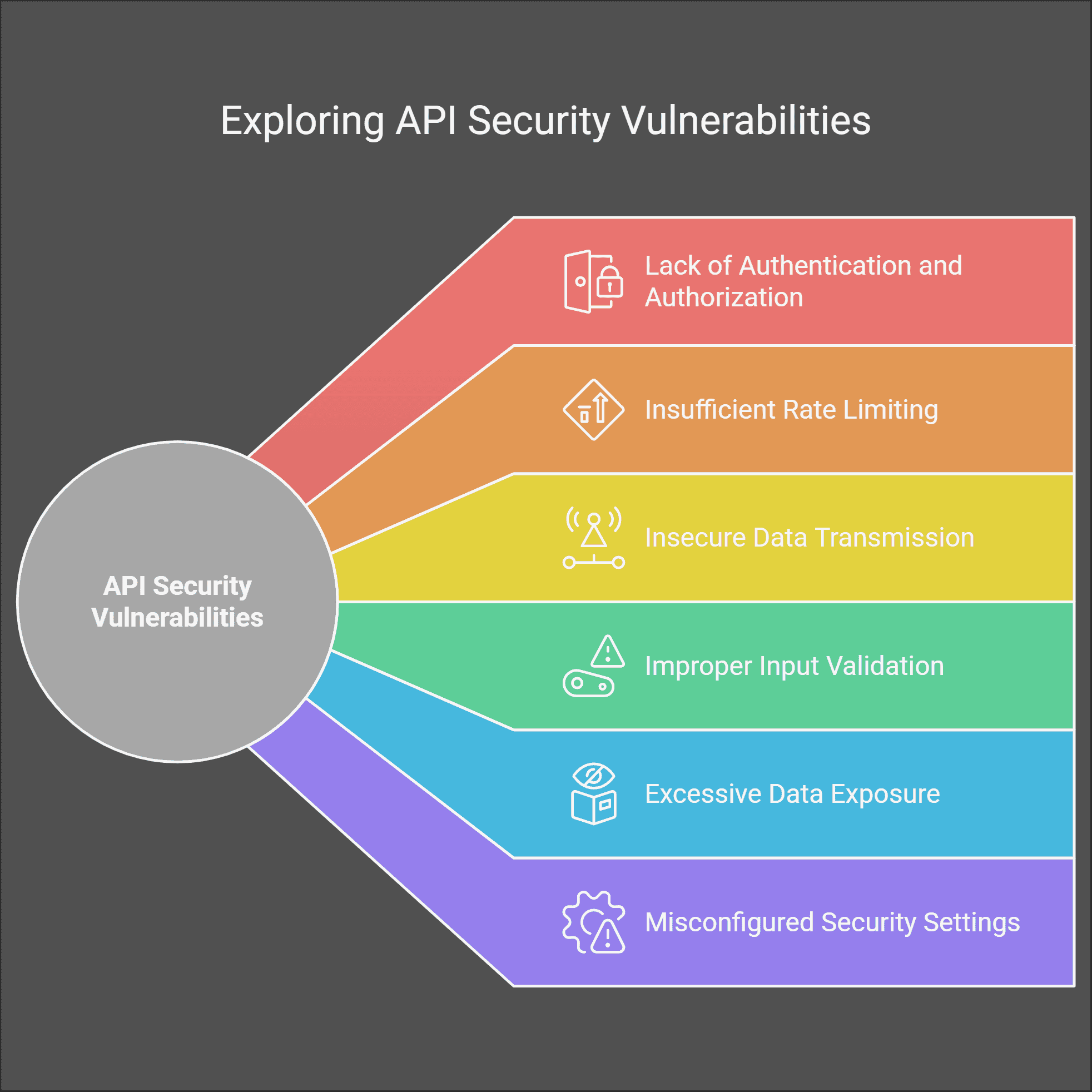
Top API Security Vulnerabilities (2026) & Fixes
Top API vulnerabilities like BOLA, mass assignment, and SSRF. Includes real breaches, fixes, and CI/CD security practices....
What Is OAuth 2.0 and How Does It Work?
OAuth 2.0 fundamentals: secure authorization framework, token-based access, and API security best practices for developers in 2026....
OAuth 2.0 Explained: Flows, PKCE & Best Practices
OAuth 2.0 essentials, Authorization Code with PKCE, Client Credentials, Device Code, plus OAuth 2....
What is OpenID Connect?
Unlock the power of OpenID Connect! Learn how OIDC simplifies online logins, enhances security, and provides seamless user experiences....
Penetration Testing: Types, Methods & Compliance
Pen testing basics and beyond: types (web, API, cloud), PTES/NIST/OWASP methods, PCI-DSS ties, tools (Kali, Nmap, Metasploit), frequency, scope......
API Inventory: Why You Need One & 10 Steps to Build It
Build a complete API inventory in 10 steps. Reduce shadow API risk, improve security posture, and stay compliant with this...